Third-party relationships with business partners, suppliers, vendors, and software providers may drive operational efficiency and innovation, but they also introduce significant security, compliance, and resilience risk. As a result, business leaders are struggling to keep up with an expanding supply chain risk universe into which they have minimal insight.
At a time when nearly 70% of functional stakeholders lack visibility into third-party risks, organizations need a reset on their third-party risk management (TPRM) programs.
Drivers of Increased Third-Party Risk
An overreliance on third parties can lead to concentration risks, where disruptions in a single vendor can have widespread consequences. This makes these points of failure attractive to threat actors who are targeting third-party relationships to exploit vulnerabilities and access sensitive data.
Regulatory requirements are also expanding, necessitating robust TPRM programs to ensure compliance with laws such as GDPR, CPRA, and upcoming regulations like NIS2 and the EU AI Act. While complying with existing rules is difficult enough, adapting to continuous regulatory sprawl presents new challenges for companies with particularly complex third-party ecosystems.
Key Program Components Across the TPRM Lifecycle
A comprehensive TPRM program includes several critical components at various stages of the TPRM lifecycle.
- Identification: Understanding the purpose and risk profile of potential third parties.
- Diligence: Conducting risk-based, actionable due diligence.
- Monitoring: Continuously managing third-party risks as their profiles change.
- Offboarding: Ensuring proper termination of third-party relationships when no longer needed.
These components are supported by enterprise-level policies, automated vendor tiering, continuous monitoring diagnostics, integration with other tools, training plans, and role/responsibility matrices.
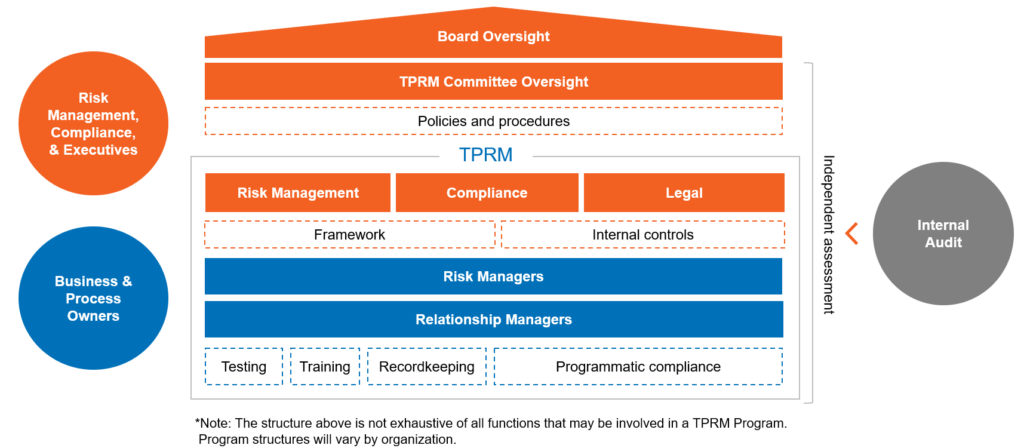
TPRM Governance Structure
Effective TPRM requires a strong governance model with clearly defined roles and responsibilities across three layers:
- Risk managers and relationship managers: Responsible for day-to-day management and oversight of third-party relationships.
- Board of Directors and TPRM committee: Providing oversight, guidance, and ensuring alignment with the organization’s risk appetite and regulatory requirements.
- Internal audit: Offering independent assurance on the effectiveness of the TPRM framework.
Common Challenges
Organizations face several challenges in implementing effective TPRM programs, including:
- Third-party inconsistencies: Duplicated efforts and irrational vendor costs.
- Missing legal and technical protections: Inadequate contractual clauses.
- Unknown and unmanaged risk exposures: Limitations in identifying and managing risks.
- Unclear roles and responsibilities: Inadequate change management and training.
- Operational inefficiencies: Lack of standardized protocols leading to shadow procurement processes.
These challenges present opportunities for transformation, however. Organizations able to harness cross-functional synergies and clearly execute on their TPRM roadmap stand a better chance of proactively mitigating risk of implementation failure.
Measuring Program Success
To measure the success of a TPRM program, organizations should track key metrics such as:
- Cybersecurity: Percentage of major cyber incidents caused by vendors.
- Resiliency: Number of vendors in financial distress.
- Regulatory compliance: Number of vendors in violation of local laws.
- Concentration risk: Percentage of critical vendors performing unique functions.
- Data privacy: Percentage of vendors with access to critical assets.
Q&A: Insights from Industry Experts
Explore frequently asked TPRM questions and answers below, sourced from common pain points and real client conversations our Integrated Risk Management team has recently had:
As organizations continue to expand their reliance on third parties, the importance of a robust TPRM program cannot be overstated. By understanding the drivers of third-party risk, establishing strong governance structures, and enhancing program success, leaders can deliver new value from the risk function.
Ready to build or optimize your TPRM program? Contact CrossCountry Consulting to get started.